Everything in the modern world is linked to the internet. Imagine if the internet was incapacitated completely for a period of time or infinitely. Suddenly, the global information system linking billions of humans would be gone. It is now almost a certainty that a Cyber Pandemic will materialise soon.
This can happen, and with multiples of threats from hackers, and organised criminal gangs who are tech savvy, the internet could be completely taken offline causing societal mayhem and chaos.
In July 2025, the WEF will conduct a live simulation that will reproduce this very event. This simulation for a Cyber Pandemic, is similar to the exercise the WEF conducted before the Coronovirus Pandemic.

Supply chain vulnerabilities are emerging as the top ecosystem cyber risk
Of large organizations, 54% identified supply chain
challenges as the biggest barrier to achieving cyber
resilience. The increasing complexity of supply
chains, coupled with a lack of visibility and oversight
into the security levels of suppliers, has emerged as
the leading cybersecurity risk for organizations.
Key concerns include software vulnerabilities
introduced by third parties and propagation of
cyberattacks throughout the ecosystem.
Geopolitical tensions shape cybersecurity strategy
 Nearly 60% of organizations state that geopolitical tensions have affected their cybersecurity strategy. Geopolitical turmoil has also affected the perception of risks, with one in three CEOs citing cyber espionage and loss of sensitive information/intellectual property (IP) theft as their top concern, while 45% of cyber leaders are concerned about disruption of operations and business processes
Nearly 60% of organizations state that geopolitical tensions have affected their cybersecurity strategy. Geopolitical turmoil has also affected the perception of risks, with one in three CEOs citing cyber espionage and loss of sensitive information/intellectual property (IP) theft as their top concern, while 45% of cyber leaders are concerned about disruption of operations and business processes
Rapid adoption of AI introduces new vulnerabilities
While 66% of organizations expect AI to have the
most significant impact on cybersecurity in the year
to come, only 37% report having processes in place
to assess the security of AI tools before deployment.
This reveals the paradox of the gap between the
recognition of AI-driven cybersecurity risks and the
rapid implementation of AI without the necessary
security safeguards to ensure cyber resilience.
Generative AI is augmenting cybercriminal capabilities,
contributing to an uptick in social engineering attacks
 Some 72% of respondents report an increase
Some 72% of respondents report an increase
in organizational cyber risks, with ransomware
remaining a top concern. Nearly 47% of
organizations cite adversarial advances powered
by generative AI (GenAI) as their primary concern, enabling more sophisticated and scalable attacks. In 2024 there was a sharp increase in phishing and social engineering attacks, with 42% of organizations reporting such incidents.
The challenge for the year ahead
The 2025 report finds that a series of compounding
factors are driving an escalating complexity in the
cyber landscape:
- Geopolitical tensions are contributing to a
more uncertain environment.
- Increased integration and dependence on more
complex supply chains are leading to a more
opaque and unpredictable risk landscape.
- The rapid adoption of emerging technologies
is contributing to new vulnerabilities and new threats.
Meanwhile, the proliferation of international
regulatory requirements adds an additional
compliance burden for organizations. All of these
challenges are compounded by a widening skills
gap, further complicating the ability to manage
cyber risks effectively.
Together, these factors drive increasing complexity
and unpredictability in the cyber landscape,
which affects organizations in many ways. First,
it drives inequity throughout the cyber ecosystem,
undermining resilience by creating a divide between
those organizations that have the resources to
adapt and those that do not and subsequently
fall behind. This affects the resilience of the
ecosystem, because many larger and more
mature organizations typically depend on extensive
networks of smaller, often less-mature suppliers,
and any incident affecting them could also impact
the entire supply chain. Second, it drives greater
demand for more specialist skills in cybersecurity,
further exacerbating the skills gap. Keeping up
with technological advances requires more specific
skills that are in greater demand in the cyber
skills market. At the same time, complexity puts
increasing pressure on often already stretched
cybersecurity teams.
These challenges demand a comprehensive reevaluation
of cyber strategies at the organizationaland
ecosystem level to address the complexity that
has become inherent in the cyber landscape.7
A broader understanding of cyber risk is necessary
that goes beyond mere “IT” and considers cyber
from an overall business risk perspective
“The rapid advancements and increasing adoption of digital
platforms globally is matched by an equally evolving cyberthreat
landscape. Cybercrime today is increasing not just in scale but also in
sophistication. As our digital footprints widen, so does the potential
attack surface for nefarious actors. It is essential that we work together
to address this growing menace. The borderless nature of the internet
necessitates collaboration across various jurisdictional limitations to
ensure that threat actors have no safe haven for their evil activities.”
Ivan John E. Uy, Secretary of Information and Communications
Technology of the Philippines
Cyberattackers are adopting new tools to increase
the effectiveness and scope of familiar forms of
attack, such as ransomware and business email
compromise (BEC). GenAI tools are lowering
the cost of the phishing and social engineering
campaigns that give attackers access to
organizations. Therefore, while the core character
of cyberattacks has remained stable, organizations
may need to place additional emphasis on
protecting themselves against well-developed
phishing and cyber-fraud campaigns.
Cybercrime-as-a-Service (CaaS) platforms
continue to be a dominant and rapidly growing
business model in the criminal landscape, allowing
individuals or groups without technical expertise to
engage in illicit online activities by purchasing the
necessary tools and support.
This model, which is already well established
among criminal groups,has progressively been
adopted in other areas of cybercrime, such
as AI-enhanced phishing attacks.
These platforms present a challenge, as they remove
the barriers for entry into cybercriminal activities.
While progress has been made in dismantling
some of the platforms, enforcement efforts remain
inconsistent as CaaS platforms continue to thrive.
The convergence of cybercrime and organized crime groups
The surge in the volume and value of cyber-enabled
fraud has attracted “traditionally” violent organized
crime groups into the cybercrime market. The
interaction of organized cybercrime with organized
violent crime groups is changing the nature of
cybercrime and greatly increasing their social impact.
This is perhaps most starkly shown by the trafficking
of more than 220,000 people to forcibly work in online
scam-farms in South-East Asia.10 With such farms
engaging in the harvesting of data, disinformation and
social engineering to name a few capabilities, they are
essentially becoming “criminal service providers”.
According to the Global Anti-Scam Alliance, scammers
have siphoned away more than $1 trillion globally in
the past year, costing certain countries losses of more
than 3% of their gross domestic product (GDP).12
The entry of traditional organized crime groups
into the cybercrime arena changes the character
of the criminal market. Organized crime groups
are accustomed to causing physical harm and are
arguably less concerned about the risk created by
attacking critical social services such as medical
services.13 When this cultural change is paired with
the scale provided by CaaS platforms, the range
of organizations that could be targeted by attacks
such as ransomware becomes wider.
“Cybercrime has persistently evolved alongside the threat landscape,
and its reach extends beyond financial loss, becoming a disruptive force
that threatens our societies. We must remain vigilant and collaborate
across sectors to safeguard the future of our digital world. Cybercrime’s
impact is far-reaching – it can halt operations, undermine confidence
and permeate to our operational technology and critical infrastructure.
In the year ahead, we must prioritize not only defence but proactive and
systemic disruption of these criminal networks as part of our collective
effort to ensure cyber resilience and protect our digital future.”
Ken Xie, Founder, Chairman of the Board and Chief Executive Officer, Fortinet
AI as a catalyst of cybercrime
GenAI tools are reshaping the cybercrime
landscape by enabling criminals to refine their
methods, and automate and personalize their
techniques. With 47% of organizations citing their
top concern surrounding GenAI as the advance
of adversarial capabilities, cybercriminals are
harnessing the efficiency of AI to automate and
personalize deceptive communications. Some
42% of organizations experienced a successful
social engineering attack in the past year, a number
that can only increase with advances and the
malicious adoption of AI.
“With emerging technologies reshaping the landscape, cyber is no longer
limited to the CIA triad: confidentiality, integrity and availability of information.
Cybersecurity now encompasses human safety and needs to address the
real risk to people’s lives when a system is attacked or compromised.”
Bushra AlBlooshi, Director of Cybersecurity Governance Risk Management
Department, Dubai Electronic Security Centre
 Escalating geopolitical tensions and increasingly
Escalating geopolitical tensions and increasingly
sophisticated cyberthreats pose significant risks to critical infrastructure, which depends on networks of interconnected devices and legacy systems. The ongoing conflict in Ukraine exemplifies these vulnerabilities, with critical sectors such as energy, telecommunications, water and heating repeatedly targeted by both cyber and physical attacks.16
These attacks often focus on disrupting control
systems and compromising data, highlighting the
critical risks associated with operational technology
(OT). As cyberthreats continue to evolve, they
not only threaten system functionality but also
jeopardize human safety, increasing the severity and
consequences of disruptions to vital infrastructure.
Some critical, high-risk areas to monitor are:
Water facilities
 Cyberattacks on water facilities pose significant
Cyberattacks on water facilities pose significant
risks to public safety, infrastructure and national
security. The Cybersecurity and Infrastructure
Security Agency (CISA) of the United States
outlined these risks in a toolkit, emphasizing the
vulnerabilities in OT systems used in water facilities, such as remote access points and outdated software.17 Cybercriminals can exploit these weaknesses to disrupt water-treatment processes, causing potential contamination, loss of service or
other hazardous consequences. A notable example
of these threats occurred in October 2024, when a
cyberattack targeted the largest water utility in the
United States, disrupting operations and raising
alarms about the security of critical infrastructure.18
Biosecurity
Rapid technological advances have redefined the
biological threat landscape, with biosecurity coming
to the forefront. The World Health Organization (WHO)
has warned that advances in artificial intelligence,
cyberattacks and genetic engineering could pose
potentially catastrophic risks to global biosecurity.19
A 2024 WHO report highlighted several ways in
which cyberthreats could compromise biosecurity,
including accessing sensitive data or research,
disruption of laboratory security systems, theft or
sabotage of biosecurity-relevant information and
espionage for competitive or harmful objectives.20
Furthermore, cyberattacks could incapacitate
essential laboratory systems, interrupting operations
and causing loss of data integrity, which would
delay critical research or compromise safety
protocols. Over the course of 2024, two laboratories
were targeted in South Africa and the United
Kingdom.21 These vulnerabilities underscore the
need for advanced cybersecurity measures in
biosecurity strategies to address these growing risks.
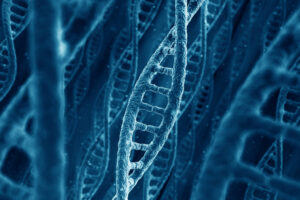 Simultaneously, the sensitive nature of genomic data poses new risks due to its unique qualities, such as the ability to identify individuals and reveal their familial ties.22 These characteristics expose genomic data to threats such as reidentification from seemingly anonymous datasets, unauthorized access leading to
Simultaneously, the sensitive nature of genomic data poses new risks due to its unique qualities, such as the ability to identify individuals and reveal their familial ties.22 These characteristics expose genomic data to threats such as reidentification from seemingly anonymous datasets, unauthorized access leading to
privacy violations and potential misuse. The breach of a genetic-testing company in late 2023 that exposed the data of nearly 7 million people
has already trained the spotlight on these risks.
Escalating complexities in cyberspace
challenge ecosystem cyber resilience
and expose gaps in preparedness
The increasing complexity of cyberspace presents
a profound challenge to achieving cyber resilience,
exacerbating inequities that leave less-resourced
organizations vulnerable. Geopolitical tensions
are prompting organizations to re-evaluate their
strategies, balancing security concerns with global
operations. Such tensions often drive targeted
attacks, as state-sponsored actors exploit
vulnerabilities for espionage and disruption. This
dynamic landscape requires adaptive strategies
that account for shifting global risks and supply
chain dependencies.
At the same time, the growing sophistication of
cybercriminals remains a persistent challenge. AI
enhanced tactics, Ransomware-as-a-Service and
advanced social engineering methods enable threat
actors to outpace traditional defences. Addressing
these evolving threats demands not only advanced
technological solutions but also cross-sector
collaboration and knowledge-sharing.
Despite these obstacles, there is cause for cautious
optimism. Organizations that embrace proactive risk
management, prioritize collaborative approaches
across ecosystems and invest in scalable, equitable
solutions can help reduce disparities. Addressing
systemic vulnerabilities – such as supply chain
dependencies and skill shortages – will be essential
to promoting a resilient digital ecosystem.
Ultimately, overcoming today’s challenges requires
not just technological innovation but a shift in
perspective. Cyber resilience must be recognized
as a collective responsibility, with organizations of all
sizes working together to fortify the interconnected
networks that underpin the digital economy. Further,
there is a need for decisive leadership action
to prioritize cybersecurity among and between
organizations; beyond technical indicators, robust
criteria rooted in the economic implications of cyber
insecurity will be required. A united leadership team,
in which business and cyber leaders see eye to eye
on the cyber risks facing the organization, is critical
to navigating growing cyber complexity.
https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2025.pdf